This guide is a simplified, Flowla-focused walkthrough derived from the official Microsoft guide, which you can refer to for full platform details.Documentation Index
Fetch the complete documentation index at: https://docs.flowla.com/llms.txt
Use this file to discover all available pages before exploring further.
Prerequisites
- Microsoft Entra user account with one of the following roles: Cloud Application Administrator, Application Administrator, Owner of the service principal
- Admin access to your Flowla workspace
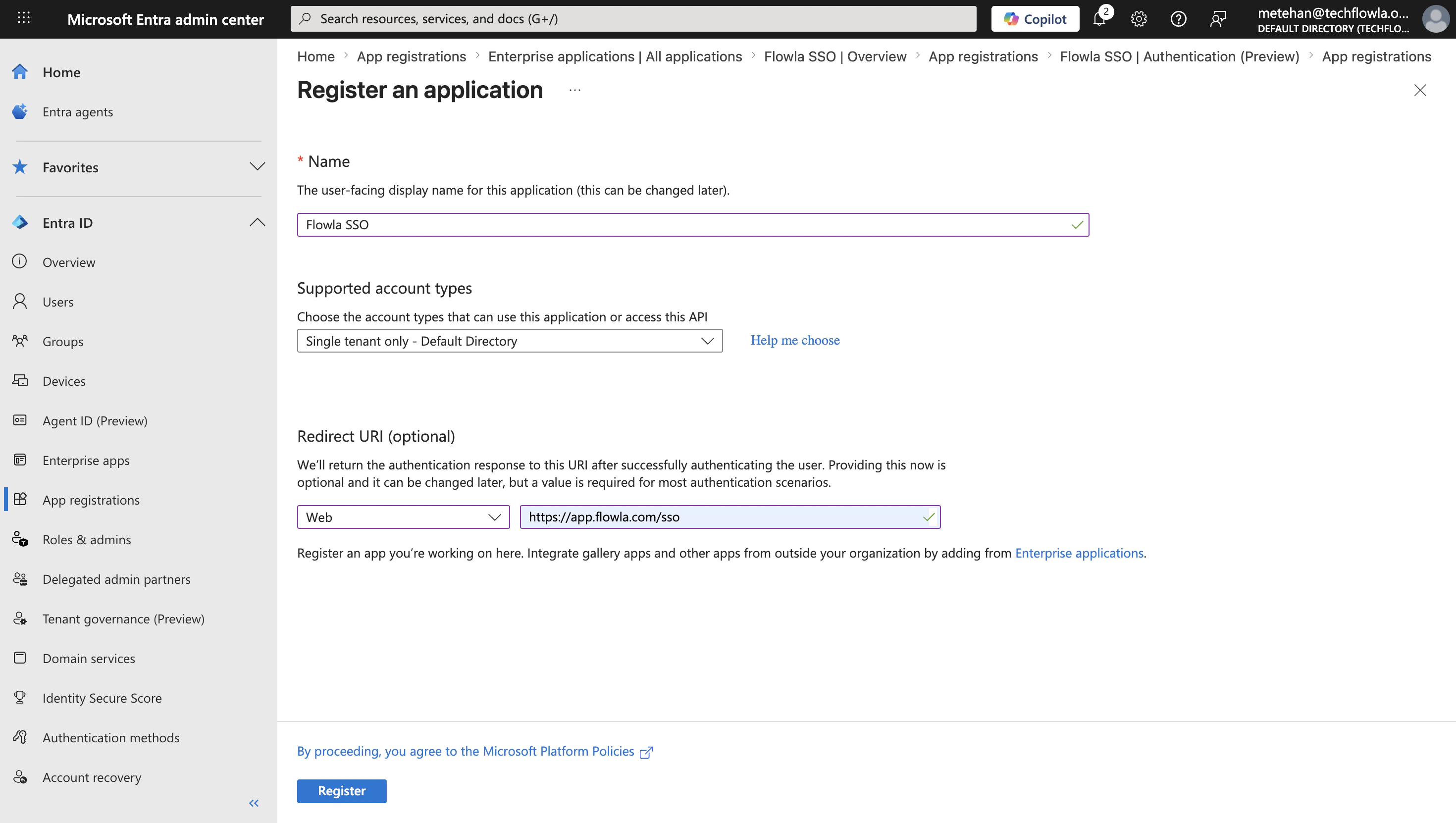
Step 1: Register your application
- Sign in to the Microsoft Entra admin center as at least a Cloud Application Administrator.
- Browse to Entra ID > App registrations > New registration.
- Enter a Name for your application (for example, “Flowla SSO”).
- Under Supported account types, select the appropriate option
- Select the platform type as Web
- Set Redirect URI as
https://app.flowla.com/sso - Select Register.
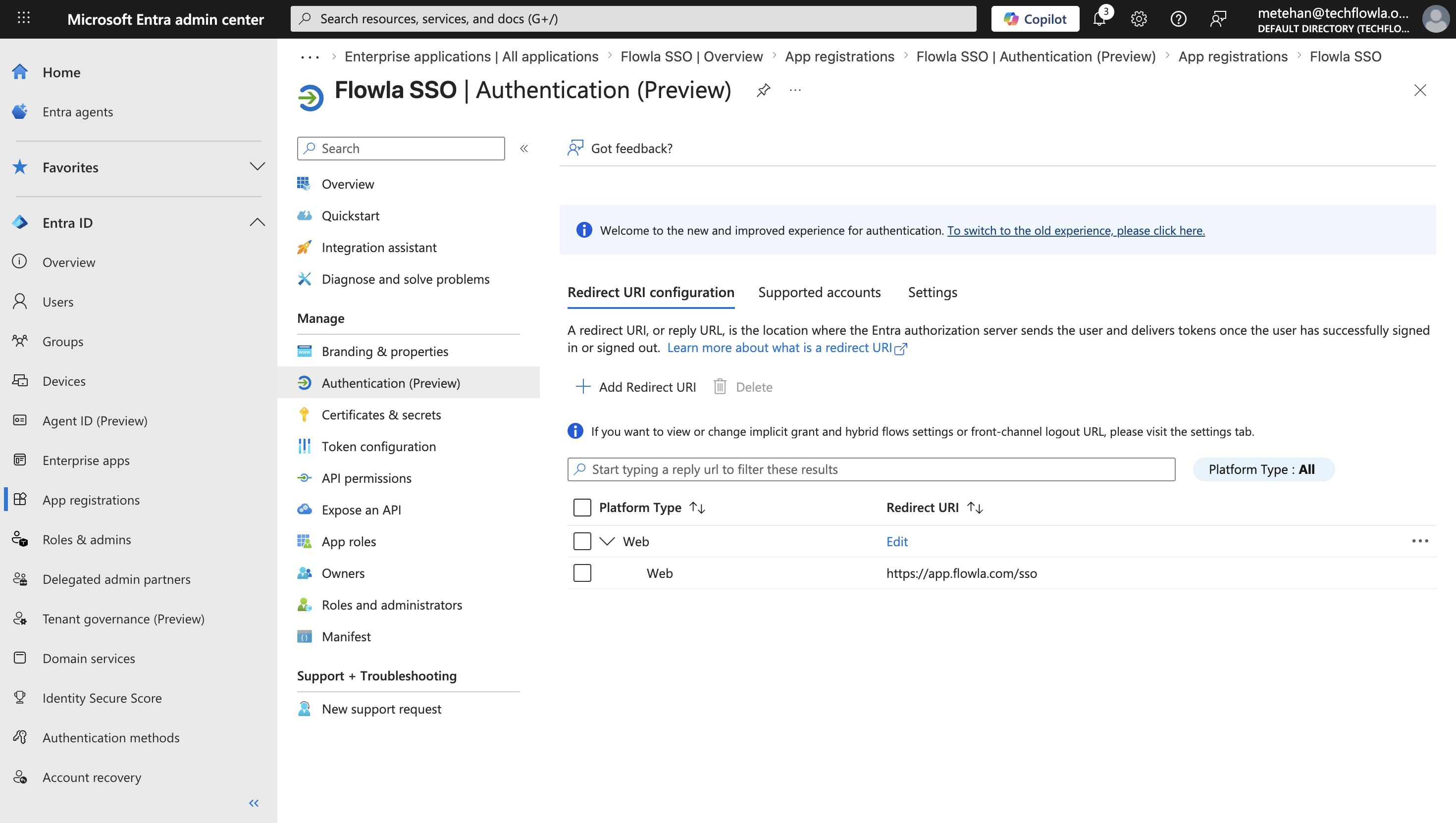
Step 2 - Configure authentication settings
- In your app registration, navigate to Authentication.
- Verify your redirect URIs are correctly configured for your platform type.
- Ensure your redirect URIs are listed under the Web platform. This option configures the standard Authorization Code flow.
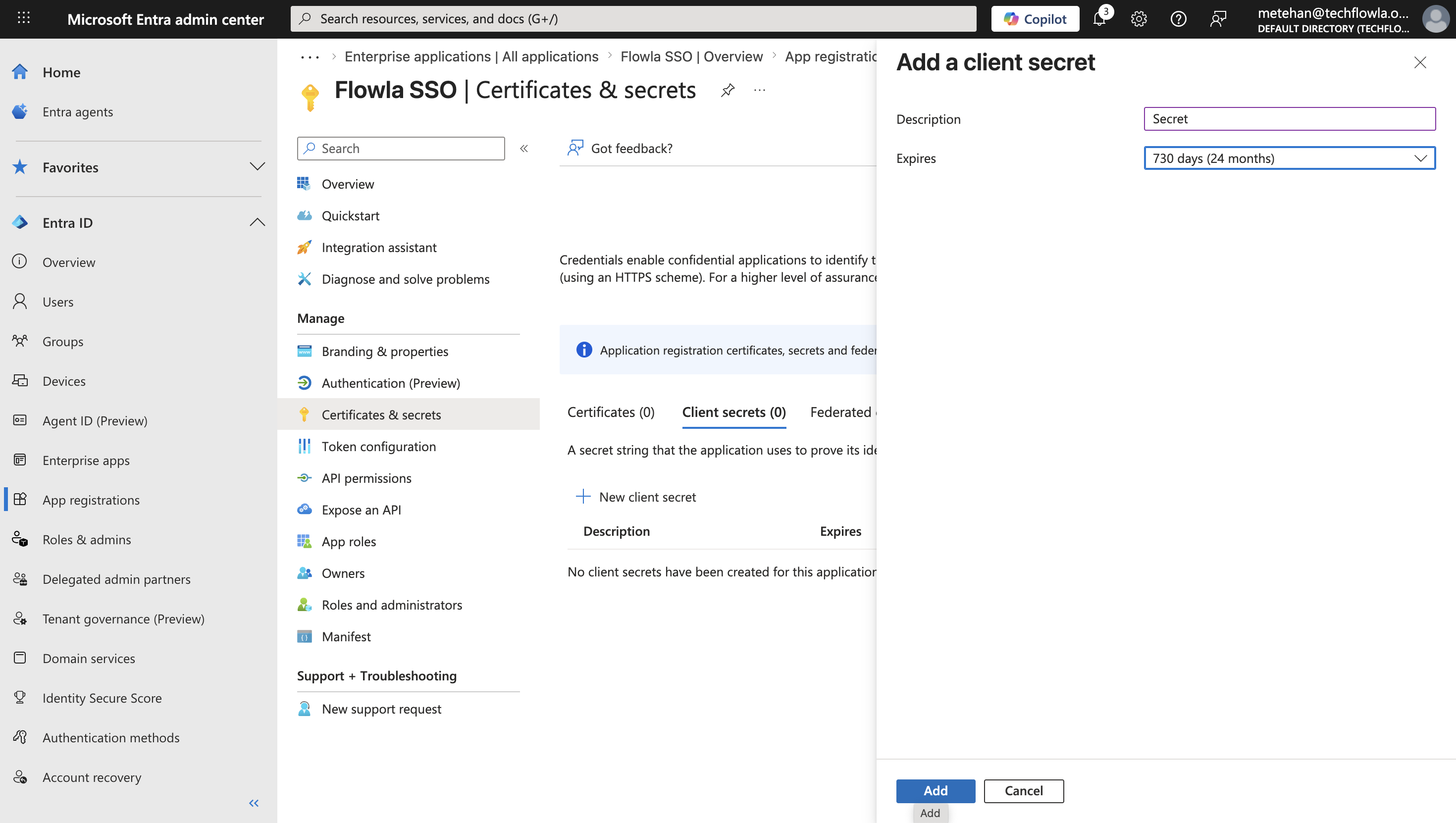
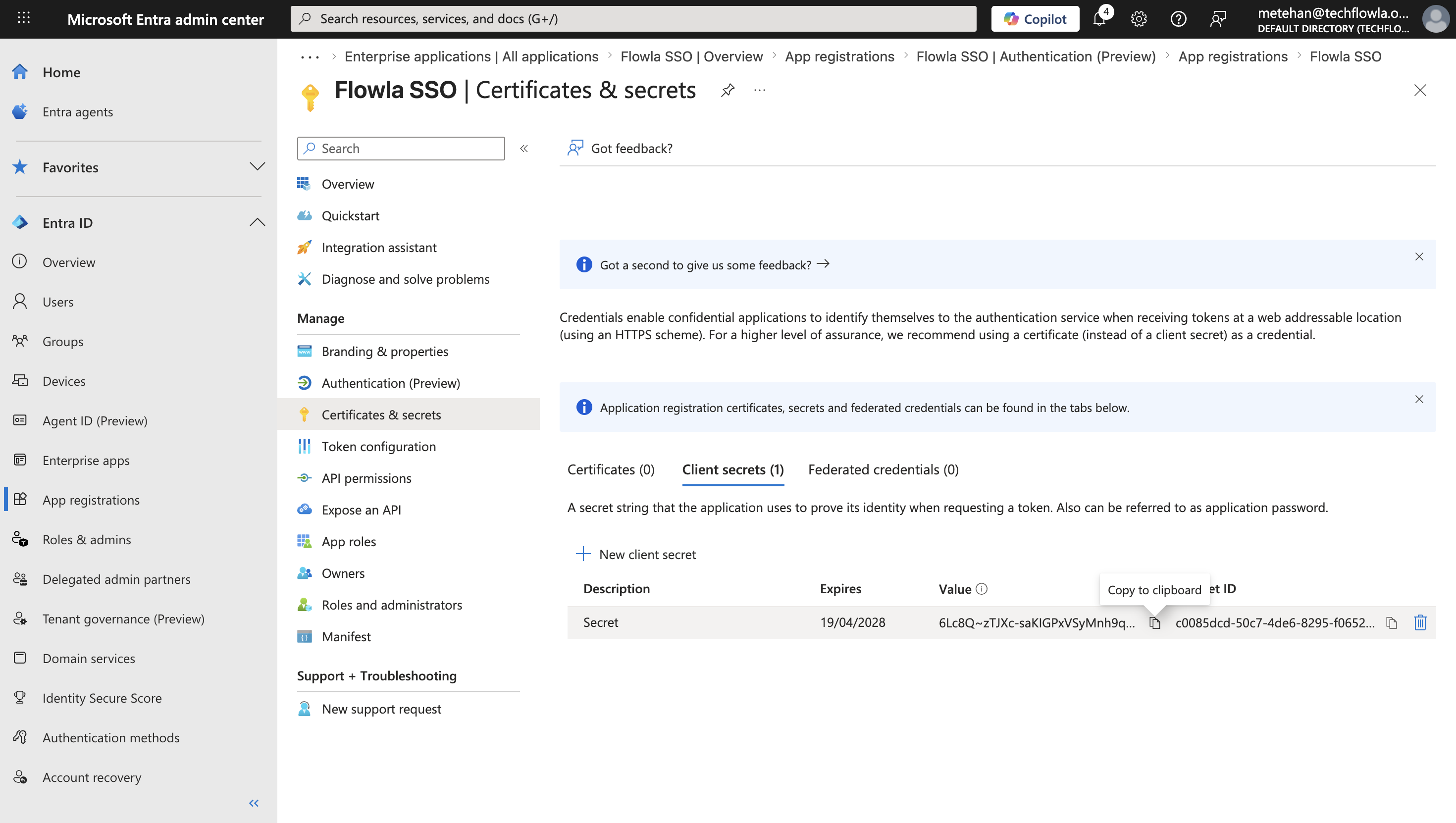
Step 3 - Configure client credentials
- Navigate to Certificates & secrets.
- Select New client secret.
- Add a description and select an expiration period.
- Select and copy the secret value immediately (it can’t be shown again).
- Store the client secret securely in your application configuration.
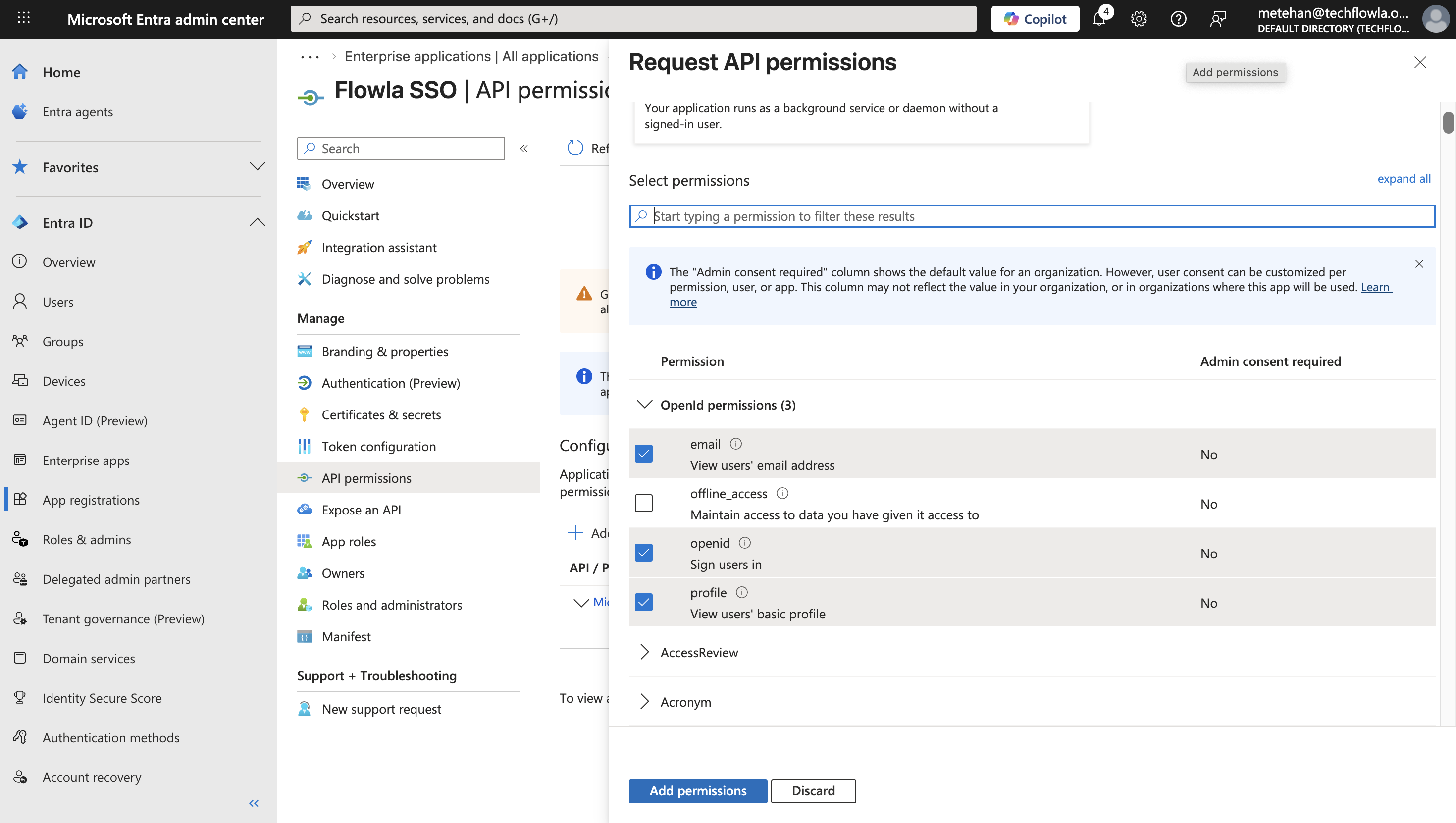
Step 4 - Configure API permissions
- Navigate to API permissions.
- Select Add a permission
- Choose Microsoft Graph
- Select Delegated permissions
- Search for and add the following delegated permissions:
openid- Required for OIDC authentication.profile- Allows access to the user’s basic profile information.email- Allows access to the user’s email address.
- Select Add permissions
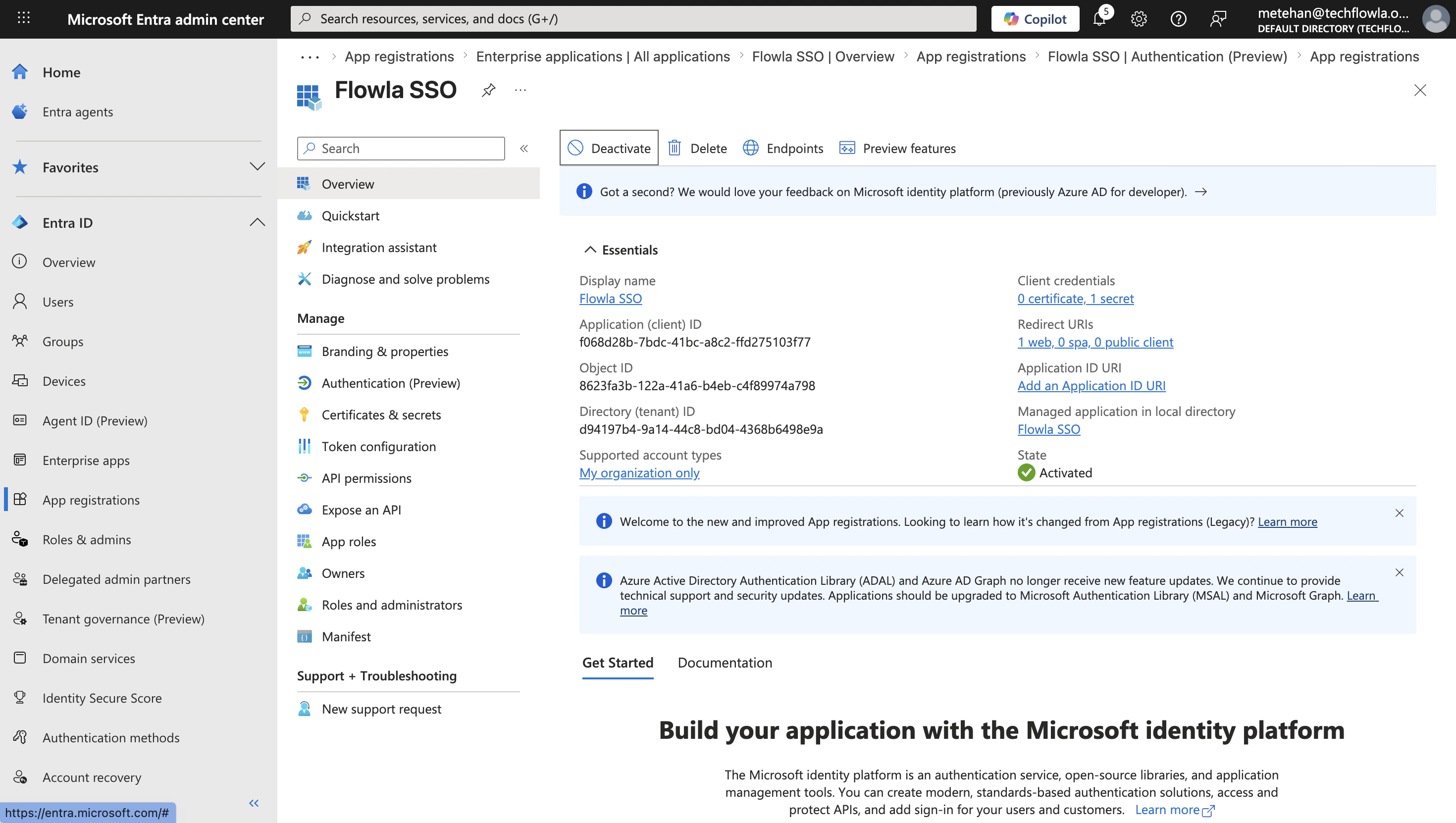
Step 5 - Gather application details
After registration and configuration, collect the following information needed for your application: From the Overview page, note:- Application (client) ID: Your app’s unique identifier
- Directory (tenant) ID: Your tenant’s unique identifier https://login.microsoftonline.com/{tenant}/v2.0/ (replace with your tenant ID)
- Client Secret Value: Your client secret’s value which created and copied in Step 3
Step 6 — Enable SSO in Flowla
In Flowla, go to Settings → Security & Permissions and click Enable SSO. Fill in the form with the values you copied from Entra ID: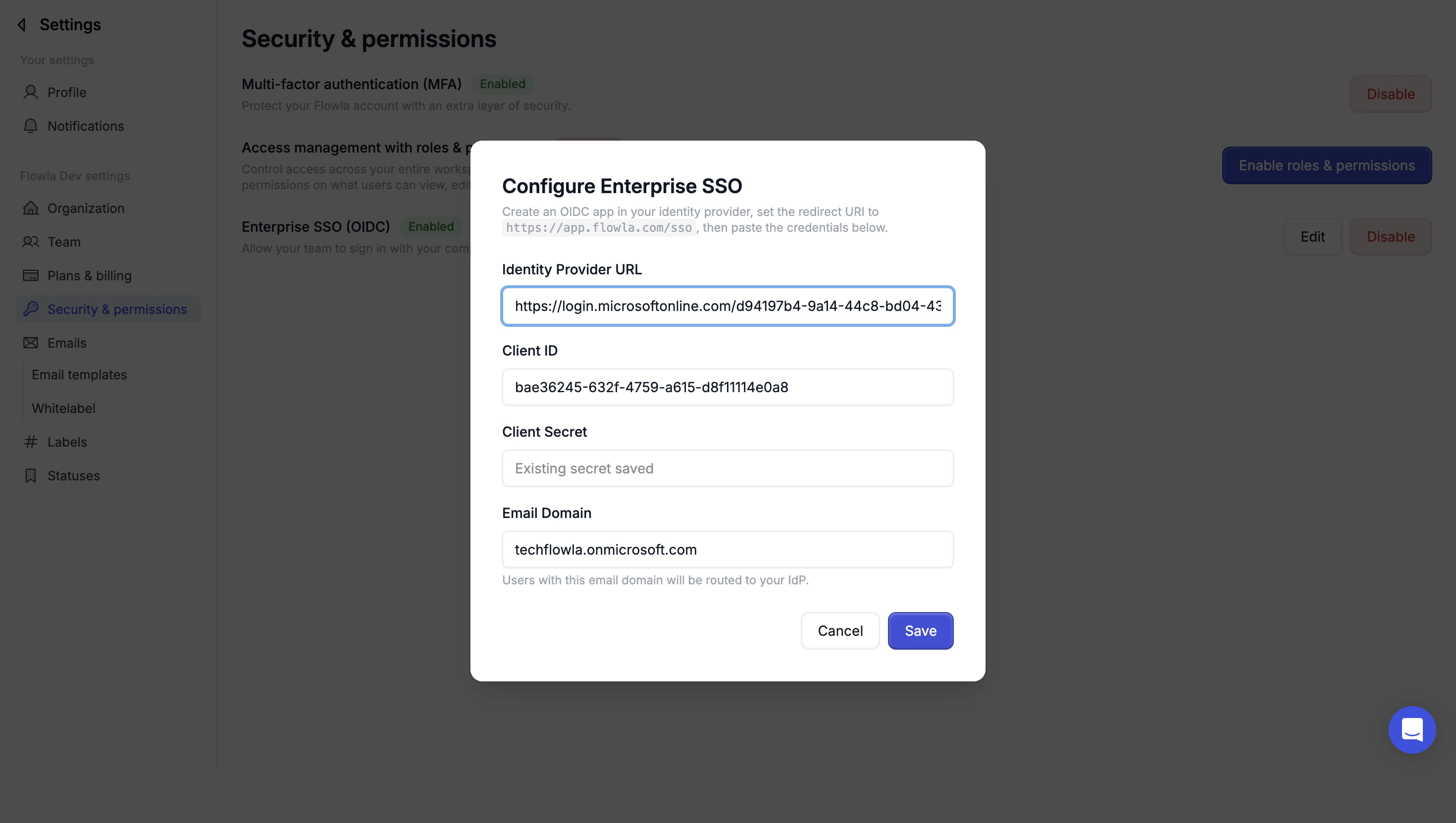
Enter your Identity Provider URL
Paste https://login.microsoftonline.com/{tenant}/v2.0/ (replace with your tenant ID)
Set your email domain
Enter the email domain your organization uses (e.g.
yourcompany.com). Users with this domain will be required to sign in via SSO.For more information, visit Microsoft Entra ID OIDC setup (non-gallery application)
Official guide for configuring OIDC SSO for a custom non-gallery application.