Documentation Index
Fetch the complete documentation index at: https://docs.flowla.com/llms.txt
Use this file to discover all available pages before exploring further.
Prerequisites
- Admin access to your Okta account
- Admin access to your Flowla workspace
Step 1 — Create an App Integration in Okta
Sign in to your Okta Admin Console, then navigate to Applications → Applications and click Create App Integration.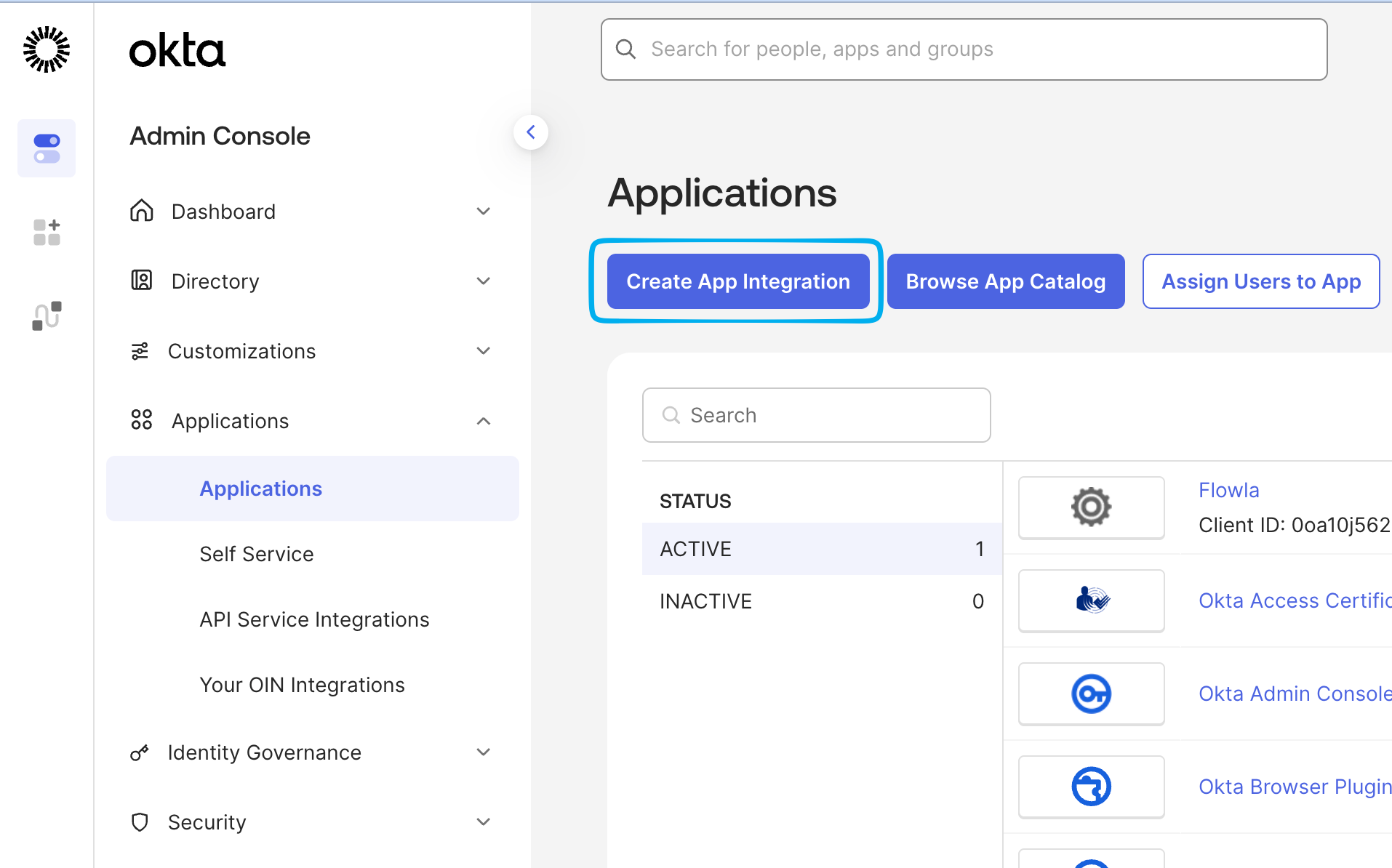
Step 2 — Select sign-in method and app type
Choose OIDC - OpenID Connect as the sign-in method and Web Application as the application type, then click Next.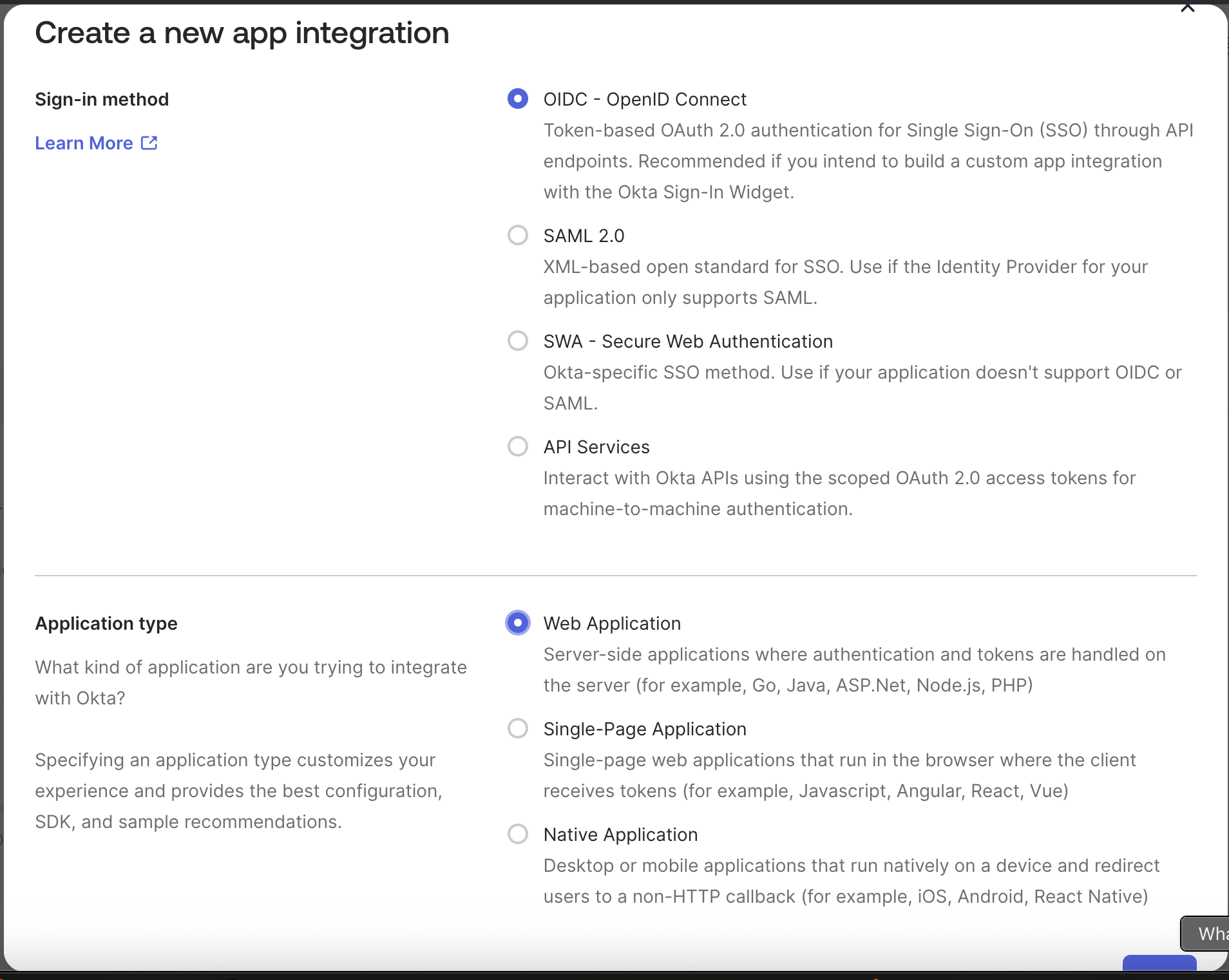
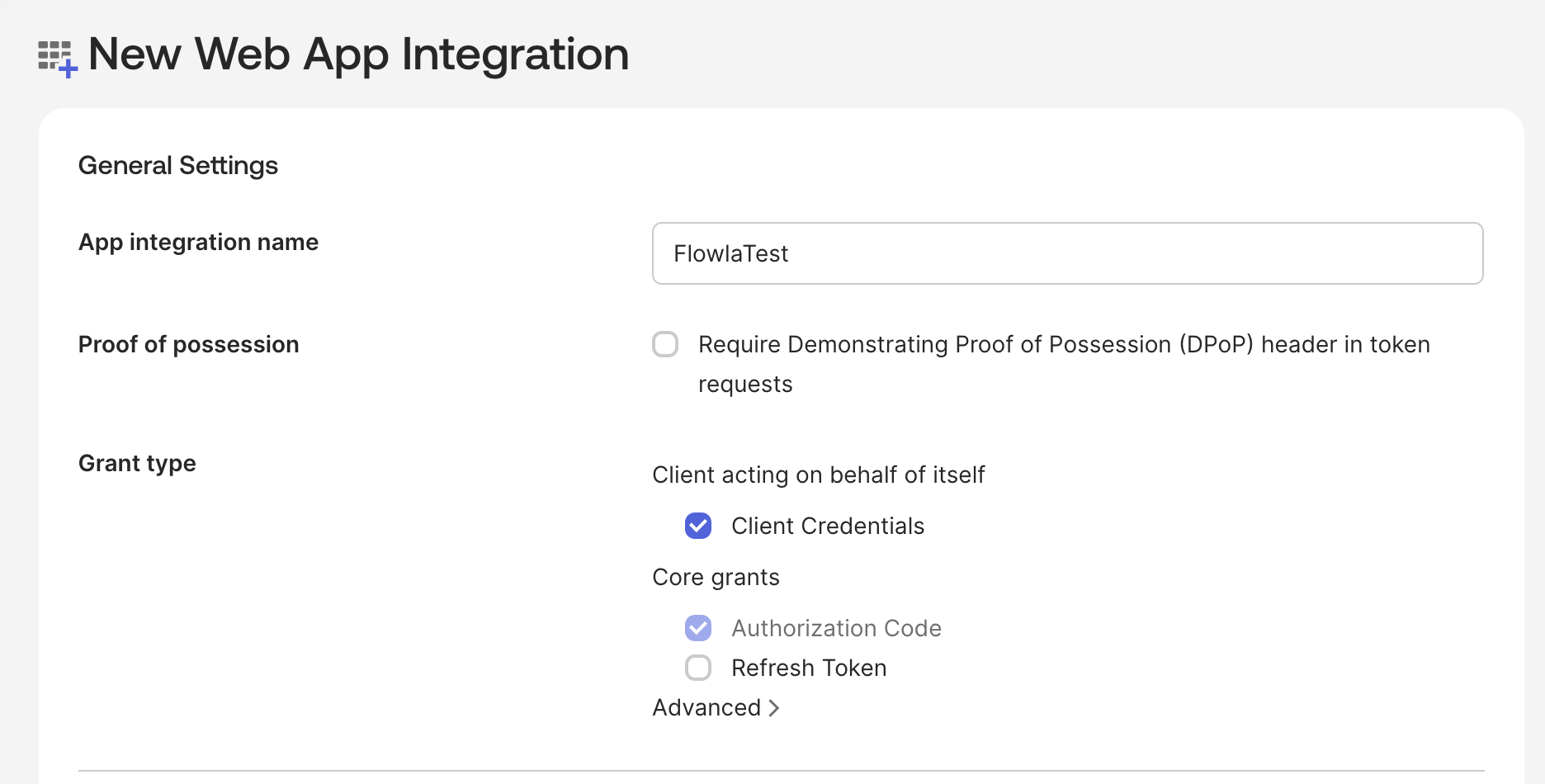
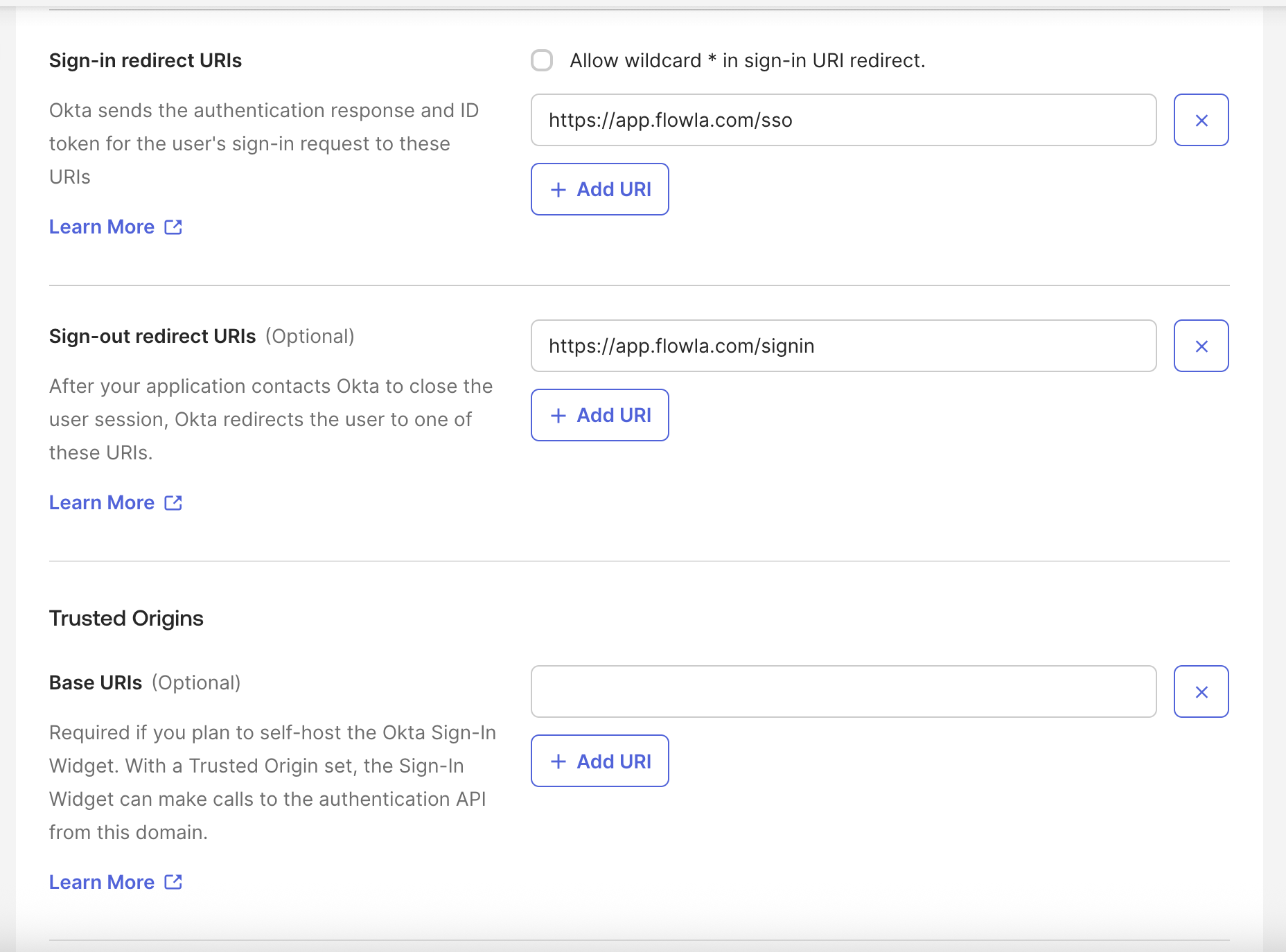
Step 3 — Configure the app integration
Fill in the following fields on the configuration page:| Field | Value |
|---|---|
| App integration name | Any name you wish (e.g. Flowla) |
| Client credentials | Enabled |
| Sign-in redirect URI | https://app.flowla.com/sso |
| Sign-out redirect URI | https://app.flowla.com/signin |
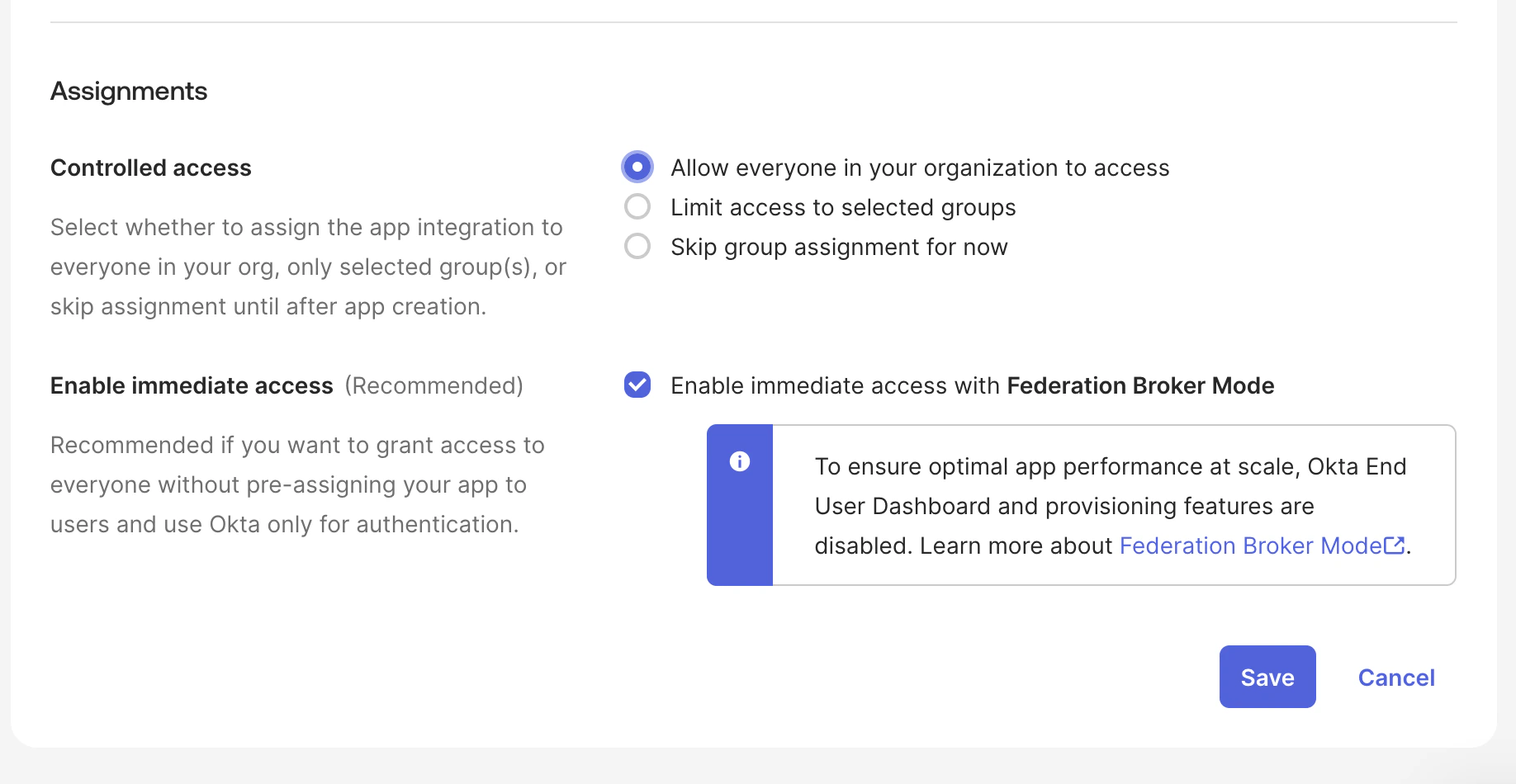
| Access | Allow everyone in your organization to access (recommended) |
| Immediate access | Enable immediate access (recommended) |
Step 4 — Copy your Client ID and Client Secret
After saving, open the General tab of your newly created app integration. Copy both the Client ID and Client Secret — you’ll need these when configuring Flowla.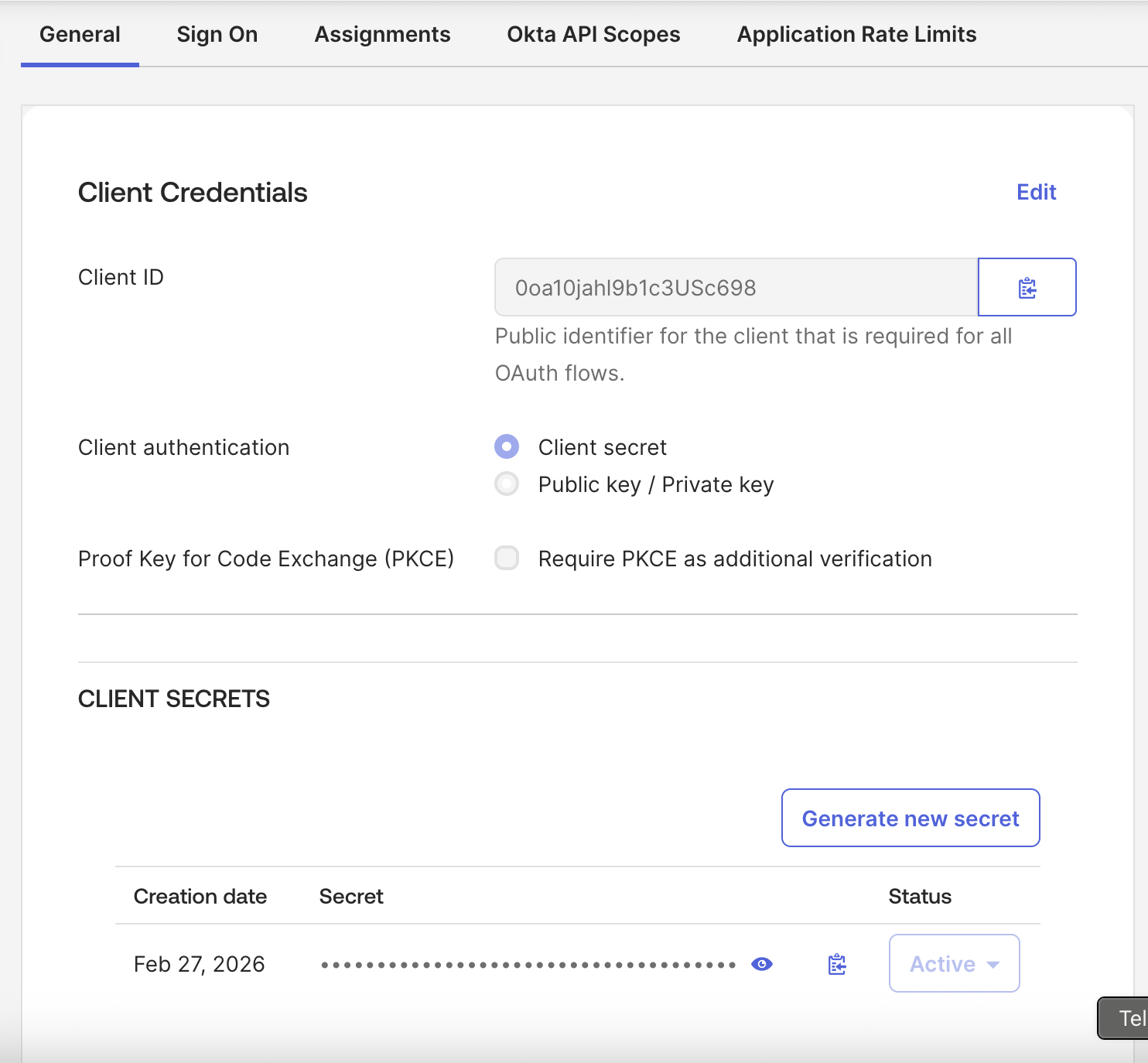
Step 5 — Find your Identity Provider URL
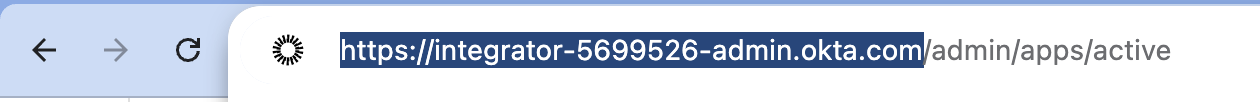
Your Identity Provider URL is the base URL of your Okta account — the part of the address bar that appears before/admin.
Step 6 — Enable SSO in Flowla
In Flowla, go to Settings → Security & Permissions and click Enable SSO. Fill in the form with the values you copied from Okta: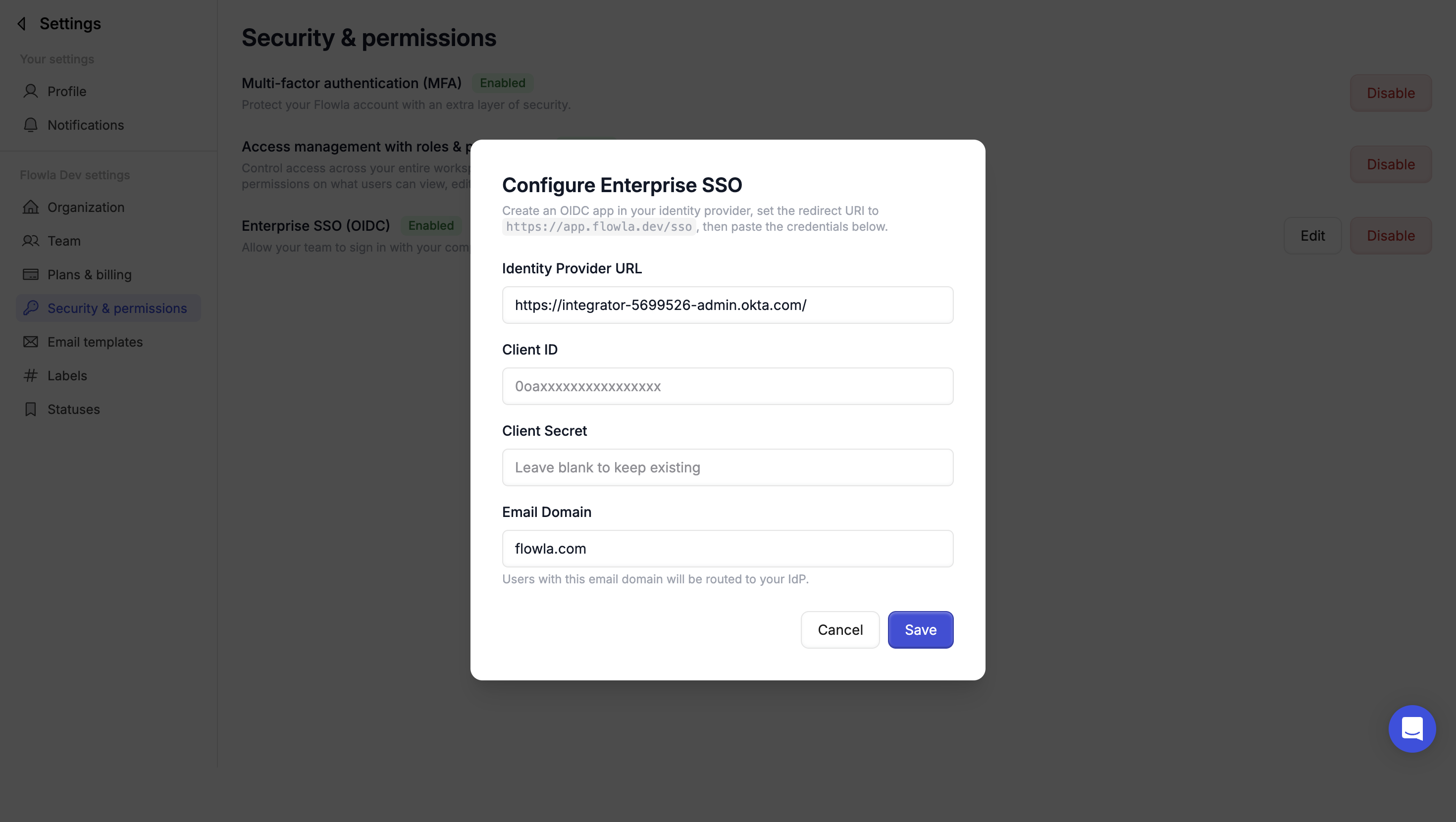
Enter your Identity Provider URL
Paste the base URL of your Okta account (e.g.
https://yourcompany.okta.com)Set your email domain
Enter the email domain your organization uses (e.g.
yourcompany.com). Users with this domain will be required to sign in via SSO.Once set up, users with your organization’s email domain will be automatically redirected to Okta when signing in to Flowla.
Troubleshooting
Users are not being redirected to Okta on sign-in
Users are not being redirected to Okta on sign-in
Make sure the email domain entered in Flowla exactly matches the domain of your users’ email addresses. Check for typos or extra spaces.
Sign-in fails with a redirect URI mismatch error
Sign-in fails with a redirect URI mismatch error
Verify that the Sign-in redirect URI in your Okta app is set exactly to
https://app.flowla.com/sso with no trailing slash.Client Secret error on save
Client Secret error on save
Okta Client Secrets are only shown once. If you’ve lost it, generate a new one from the General tab of your app integration in Okta, then update it in Flowla.
Only some users can sign in via SSO
Only some users can sign in via SSO
Check the Assignments tab of your Okta app integration. If access is not set to Everyone, individual users or groups may need to be explicitly assigned.